You can now personalise the Workflow Collect interface with your own customization. This configuration is currently done via the Yousign app only.
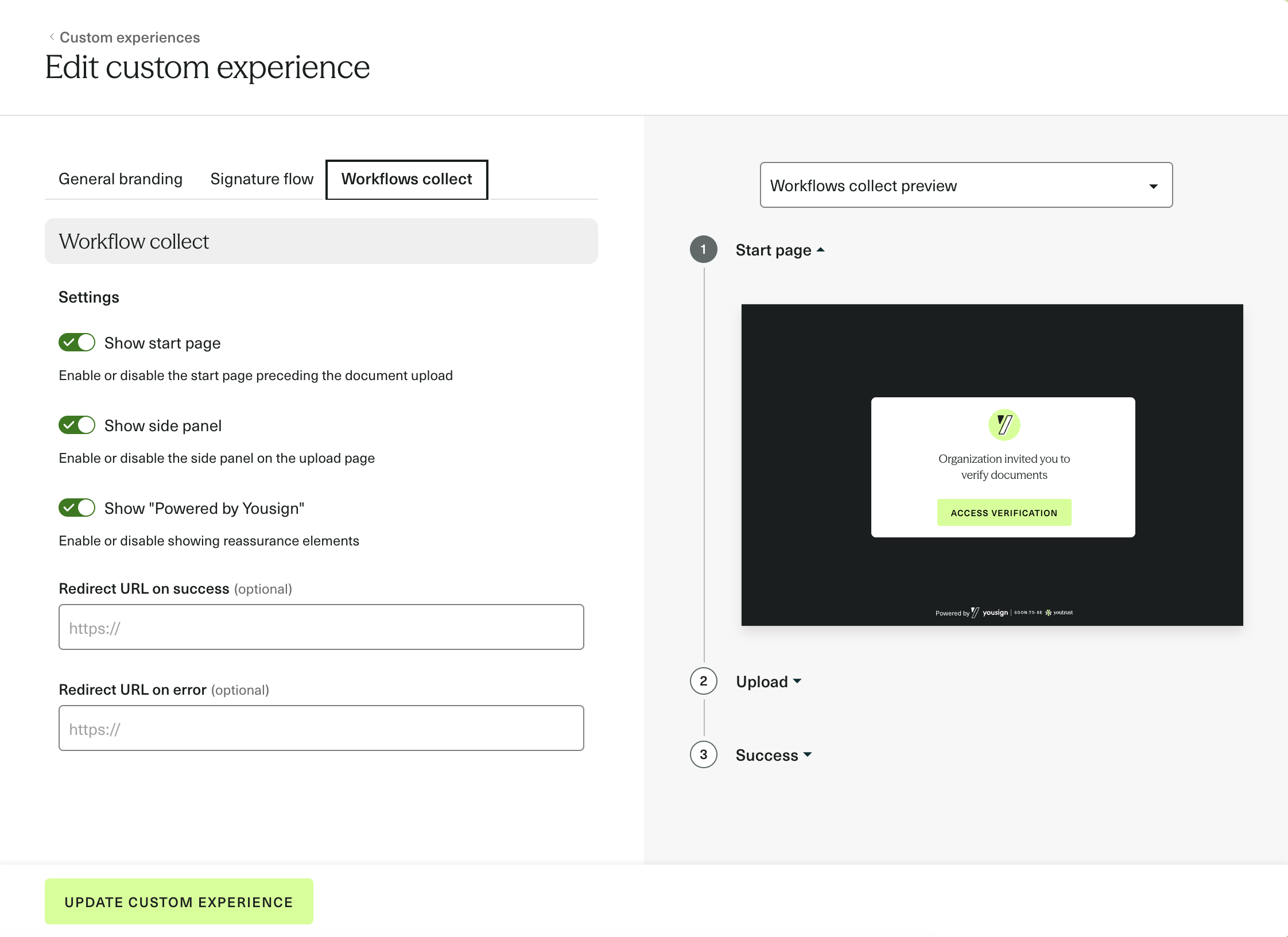
The following settings are available:
- Branding: company logo, background color, text color, button color
- Flow settings: show/hide the start page, show/hide the side panel, show/hide the "Powered by Yousign" badge
- Redirect URLs: custom redirect on success or on error (optional)
Any update made to the Custom Experience in the app is reflected instantly across all Workflow Sessions using the associated template.
Learn how to set it up in the guide.